March 27, 2026 • 12 min read
Data regulatory compliance: A CISO’s strategic framework

Mitchell Nazarov
CISOs today face a growing number of data governance, compliance, and regulatory requirements across every industry and size. The acceleration of business technologies and the exponential growth of customer data have spurred governments to issue regulations on data security, privacy, and compliance. These data protection laws are designed to safeguard and preserve sensitive information, address data breaches, and protect individuals’ data.
Often, CISOs are tasked with managing the complexities of multiple data governance frameworks.
Understanding the regulatory landscape
In addition to established regulatory compliance requirements like GDPR, HIPAA, SOX, PCI DSS, FISMA, and regional and state-level requirements in over 20+ states like CCPA, as well as optional data compliance standards like ISO 27001 and SOC, CISOs face emerging laws and the challenge of balancing existing data compliance measures while implementing new controls to address risks in an evolving landscape.
Overview of data governance regulatory requirements
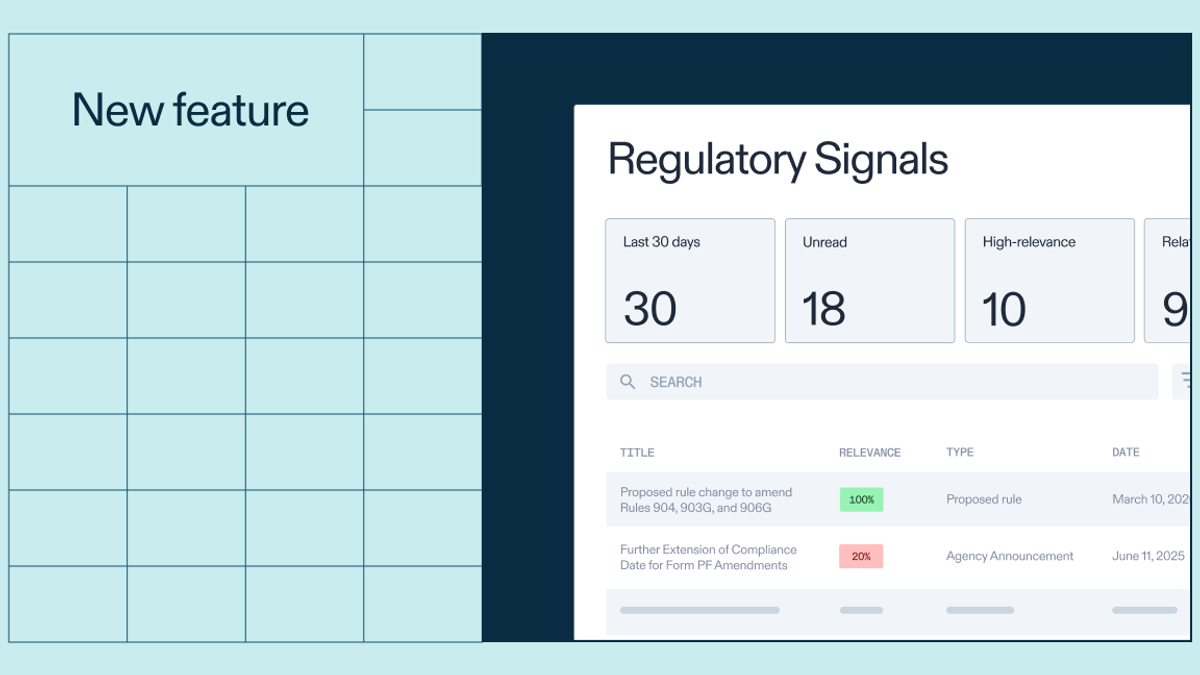
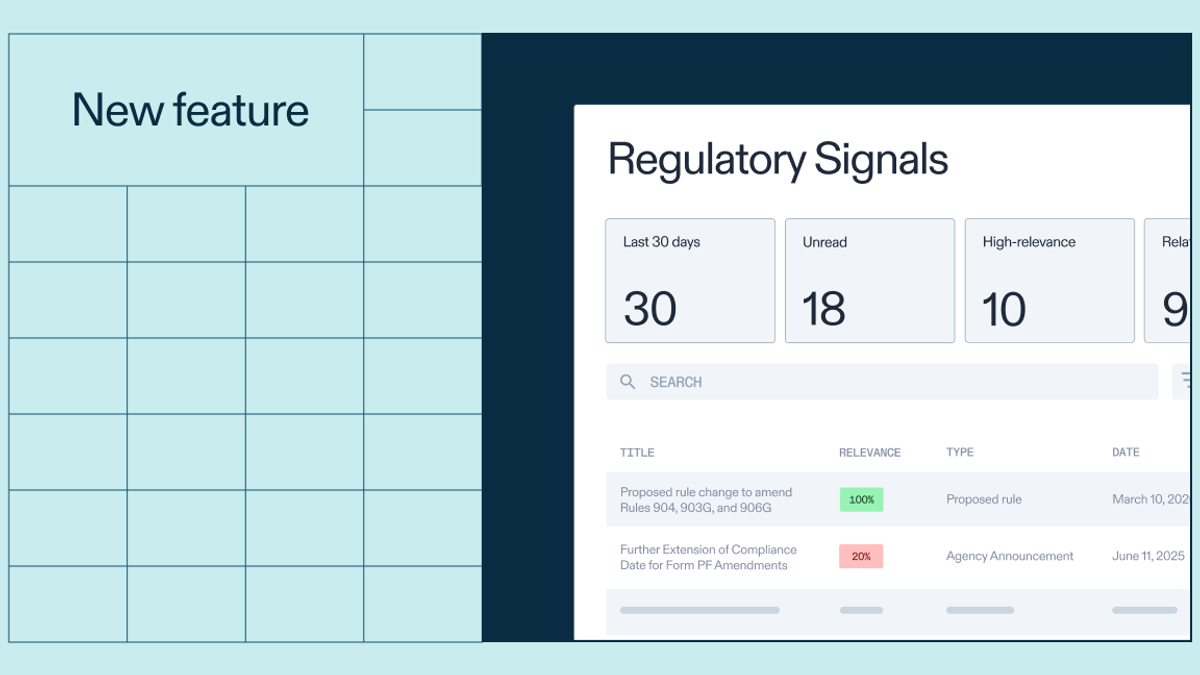
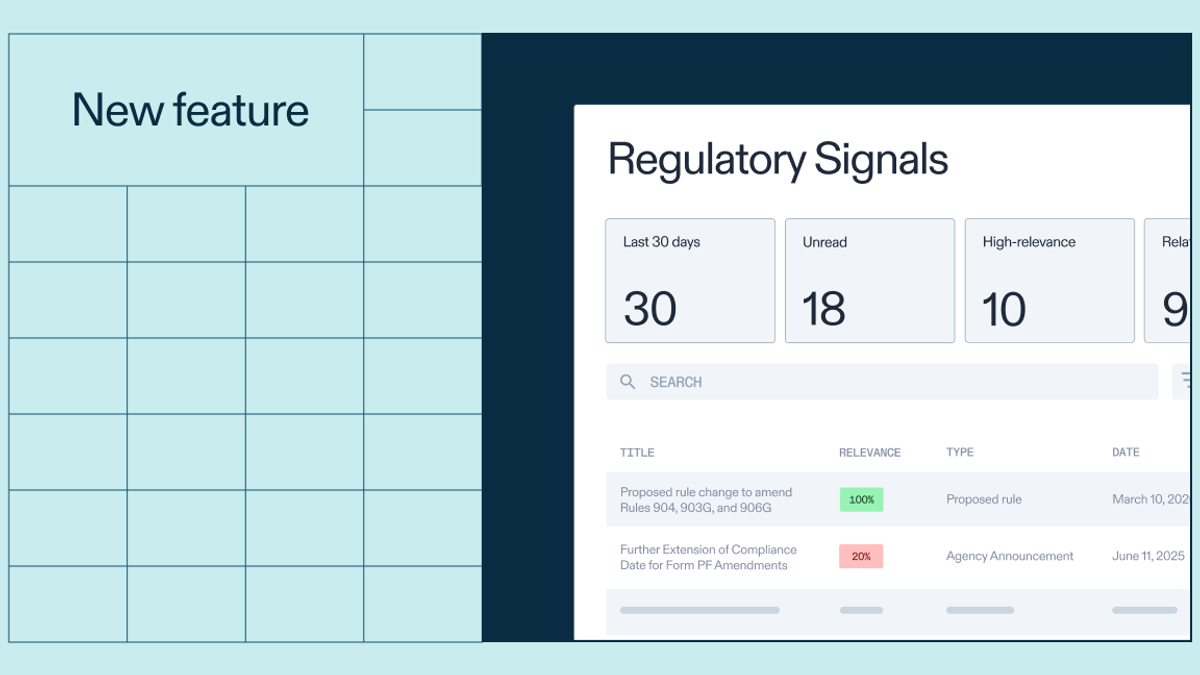
CISOs can leverage tools like Optro and subject matter expertise to better address multiple, overlapping regulatory requirements. The table below provides an overview of data governance standards and frameworks that CISOs should be familiar with.
GDPR vs. CCPA
The EU has established the overarching General Data Protection Regulation (GDPR) to address data governance and set forth privacy laws that apply to all EU personal data. The United States has not yet opted for a federal or overarching privacy law to address all US personal data, individual states within the US have. The California Consumer Protection Act (CCPA) broke ground and established regulatory requirements for the data handling and data processing of California residents’ sensitive information.
Both regulations are aimed at giving individuals greater control over their data, and they establish privacy rights for personal information. Some of the differences between the GDPR and CCPA include:
- Scope: The GDPR affects the entire EU, as well as organizations that handle EU resident information. The CCPA protects California residents’ data only.
- Data collection: The GDPR focuses on requiring explicit consent to collect data (cookie acceptance pop-ups are one example of this in action). The CCPA focuses on the option to opt out of data collection and data sharing. By default, collection is allowed for CCPA.
- Types of organizations affected: The GDPR affects all organizations handling EU resident data. The CCPA applies to for-profit organizations that meet certain thresholds related to revenue, collected data, and the selling of data.
Both regulations provide an avenue for enforcement that includes penalties and fines. These penalties can be significant.
Emerging laws and evolving standards
Beyond existing laws that are already in place, CISOs must keep an eye on the future, anticipating the evolution of existing standards and paying attention to regulations on the horizon. With the rise of AI and continued adoption of cloud-based solutions, CISOs should anticipate changes to existing regulations — those that have been announced, and those that are being drafted.
Some emerging laws CISOs should pay attention to include:
- Regional and State Privacy Laws for applicable geographic areas
- Updates to the HIPAA Security Rule and HIPAA Privacy Rule
- NIST CSF 2.0 release
- Proposed changes to the GDPR
- The Cyber Resilience Act (CRA): Mandatory reporting of actively exploited vulnerabilities beginning in September 2026
CISOs may even want to provide their comments on upcoming regulations, which is permitted during the drafting phase of most data governance frameworks.
Key challenges CISOs face in data compliance
Each of the regulations and standards covered in this article has unique and overlapping requirements. CISOs must tackle the challenge of deciding which frameworks to implement and how to implement controls and security measures that most efficiently and effectively meet data governance requirements.
With limited resources and expertise and the expansion of regulatory requirements, alongside how compliance is often seen as a cost center rather than an innovation center, CISOs have many obstacles they need to navigate.
The functions under CISO oversight are manifold and involve many moving parts. A CISO's responsibilities might include:
- Contributing to company strategy and risk management, especially in the area of information security
- Accounting for all regulatory requirements that affect information systems
- Performing risk assessments for information systems
- Establishing security for all types of data, including sensitive and legally protected data
- Addressing gaps related to information security or risk management
- Preventing data breaches
- Responding to security events and incidents
- Selecting applicable risk management and cybersecurity frameworks and methods to apply at their organization(s)
Cross-functional collaboration is a necessity when implementing security measures such as data access and authentication controls, incident response plans, data storage, deletion, and processing policies, and other controls required as part of the greater organization’s compliance program. On top of that, CISOs and their teams are often in the thick of day-to-day business operations, working to secure cloud services, prevent the risk of data breaches, and handle unauthorized access as it arises.
Orchestrating all of these disparate efforts across the organization while catching important privacy and security compliance details is one of the key challenges CISOs face today in data compliance and governance.
CISOs need technology and tools that can enable success across various compliance workstreams. They need tools that can give them the right information for the right frameworks at the right time to streamline their operations and prioritize the data practices that have the most impact. They need value-added reporting that facilitates clear and effective decision-making.
Optro is uniquely equipped to provide CISOs with the utilities and capabilities that will help them achieve effective and efficient compliance without gaps.
Optro’s role: Centralizing compliance governance
Optro is an all-encompassing GRC tool that supports multiple frameworks. With that multi-framework support, CISOs can see what compliance requirements are key and which overlap, allowing them to identify and tackle high-value, high-impact data governance targets. Through Optro, CISOs can have a centralized view of compliance and regulatory standards and corresponding controls in place to quickly locate vulnerabilities and increased risk areas.
Building a future-ready compliance roadmap
The insights, reporting, mappings, and references provided through Optro’s solution give CISOs a single pane of risk to inform decision-making and build a roadmap. From Optro, CISOs can assign tasks and communicate with their teams, tackling the foremost problems on their list. And with Optro's robust risk management reporting and dashboards, CISOs can track KPIs and open issues with ease.
KPIs for security compliance and data governance
Key performance indicators (KPIs) for data governance and risk management differ vastly across organizations. Organizations may opt to track risks as a whole or break them down into discrete projects with different teams. Organizations might choose to track one framework versus another. Optro’s pre-built and customizable dashboard options allow CISOs to track the metrics that matter to them. Reporting out of Optro is simple: The platform is designed to export customizable visuals for target stakeholders, including at the team and executive levels.
Embedding automation for evidence readiness
Optro’s automated evidence collection, supported library of 30+ frameworks, and out-of-the-box integrations can be invaluable tools for CISOs when preparing for audits, whether they are internal or external. Integrated and automated evidence collection, in combination with cross-framework control mappings, shows security compliance teams where gaps exist and where evidence needs to be provided.
Through customized dashboards and automated evidence collection, Optro helps CISOs stay audit-ready and operationally ready to take on risks when they arise, as well as provide organizational leadership with valuable data, reporting, and results.
From chaos to control
At InComm Payments, the CISO’s team was managing PCI DSS, SOC, and other security requirements through scattered spreadsheets, disconnected audits, and constant manual evidence requests. The process was slow, repetitive, and offered little visibility into real compliance gaps.
After moving to Optro, the CISO organization centralized its security controls, evidence, and framework mappings in one place. The shift cut IT evidence requests by 50%, reduced security audit cycles by two weeks, and eliminated redundant work tied to overlapping frameworks. With automated evidence collection and consistent reporting, the team gained a clearer view of compliance health and could prepare for audits without the last-minute scramble.
InComm’s experience shows how Optro helps CISOs build a more stable, efficient compliance program — one that stays aligned with requirements and avoids the fire-drill approach.
Request a demo today to see how your team can do the same.
About the authors

Mitchell Nazarov, M.S., CDPSE, works on Optro’s implementation team specializing in compliance. Prior to joining Optro, Mitchell spent 5+ years scaling up GRC programs, vulnerability management teams and leading information security and compliance audits in the application security and healthcare industries. Mitchell specializes in cybersecurity audits, NIST frameworks, SOC 2, enterprise risk management, and software implementations. Connect with Mitchell on LinkedIn.
You may also like to read

How to choose the right regulatory compliance tool for 2026

Healthcare regulatory compliance: What IT compliance managers must know
Regulatory Horizon Scanning: Why proactive compliance is no longer optional

How to choose the right regulatory compliance tool for 2026

Healthcare regulatory compliance: What IT compliance managers must know
Discover why industry leaders choose Optro
SCHEDULE A DEMO


